Resetting Admin Password on a Cisco ISE Appliance
A great little "feature" of Cisco's Identity Services Engine is that out of the box, the administrator account expires after 45 days if the password is not changed during that time. The documentation says that if you have trouble logging in you should click the "Problem logging in?" link and use the default administrative user/pass. This is of course ridiculous and does not work.
Below are the steps for properly resetting an admin password and for changing the security policy so the lockout doesn't happen again.
ISE systems can be installed on dedicated server hardware or as virtual appliances under VMware vSphere. The box in my lab is a virtual appliance so these steps are going to reflect console access and rebooting of a VM.
#1 - Reboot from ISE DVD/ISO⌗
Update Oct 18 2015: This step is only necessary if you're also locked out of the CLI. If you have a working CLI username/password, skip to step #3. If your CLI username/password aren't working, you need to do a full password reset by following the steps below to get to the recovery console.
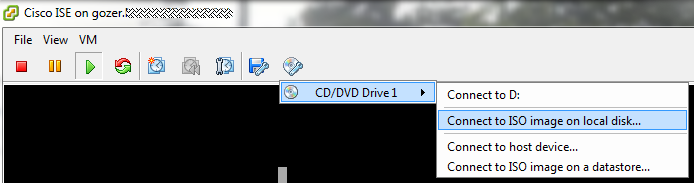
To get to the recovery console, the appliance needs to be booted from the ISE installation media. I had the ISO image handy so I used that. Now under vSphere, when the VM reboots, any media that was attached prior to the reboot is disconnected. The trick is to have the console window for the VM open in vSphere Client and hit the <F2> key when you see the VMware BIOS screen. With the machine sitting in the BIOS, it gives you time to reattach the ISE ISO to the DVD drive before the OS starts to load up.
Also while in the BIOS, adjust the boot device order so it hits the CD-ROM drive before the hard drive.
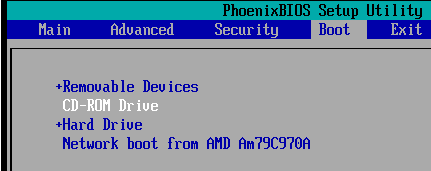
If you're doing a recovery on a physical appliance, you'll probably still want to check your boot device order and also set it to boot from CD/DVD drive first.
Save your BIOS changes and boot the machine.
#2 - Reset Admin CLI Password⌗
When the machine boots from the ISE DVD it will display a number of boot options.
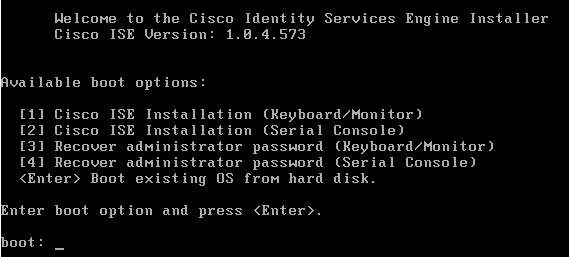
If the appliance is a VM or is a physical appliance with a keyboard/mouse attached, choose #3. If the appliance is accessed via a serial console, choose #4.
The recovery menu now appears and asks which admin account to recover.
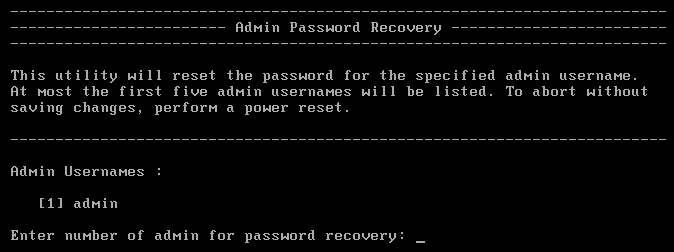
Choose the account and enter a new password. This password will be used to log in on the appliance's console. It does not work on the web UI.
Reboot the appliance now, making sure to eject/disconnect the DVD/ISO image so that it boots normally.
#3 - Reset the ISE GUI Admin Password⌗
With the appliance booted normally, log in on the console using the CLI admin account. Remember: the console admin account is different than the web UI admin account. They have the same username but can have different passwords.
From the command prompt, use the command "application reset-passwd ise admin" to set a new web UI admin password.
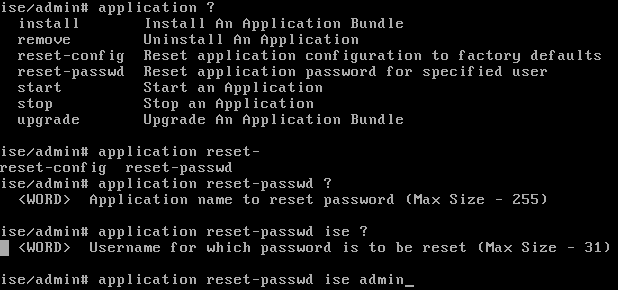
The screenshot above shows other options that can be used with the "application" command.
The web UI should now be accessible using the password that was just set.
Change the Password Lockout Policy⌗
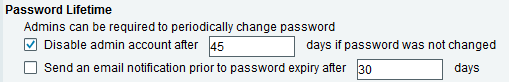
The default password policy says that admin accounts will be locked out if their passwords are not changed once every 45 days.
The lockout policy can be adjusted by navigating to Administration > System > Admin Access > Authentication > Password Policy.
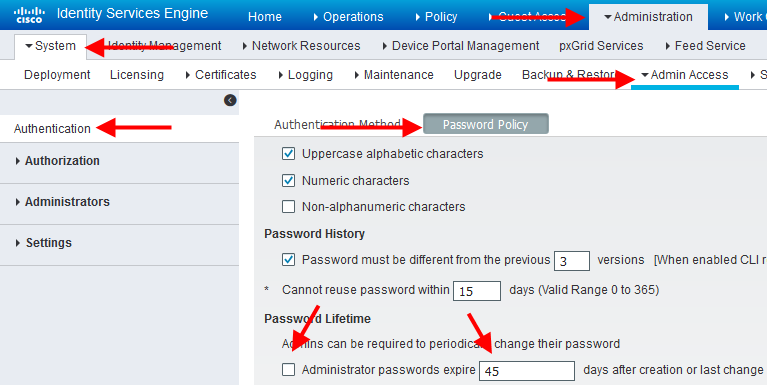
The Password Policy screen hasn't changed since ISE v1.1 and should work in all current versions of ISE.
Did I Need to Reset the CLI Admin or Am I Just Forgetful?⌗
I confess, I'm not 100% sure that I needed to reset the CLI admin password. None of the passwords in my password safe were working on the CLI so it was either expired or I forgot to store the CLI password in the safe. If your web UI password doesn't work, try starting from step #3 to see if you can avoid rebooting the appliance. Best case it works, worst case you start from step #1 and reset all the passwords.
Update Oct 18 2015: Thanks to dileep and Joe S who commented that the CLI password is separate from the web UI password and that as long as you still have access to the CLI, there's no need to do a full password recovery.
Disclaimer: The opinions and information expressed in this blog article are my own and not necessarily those of Cisco Systems.