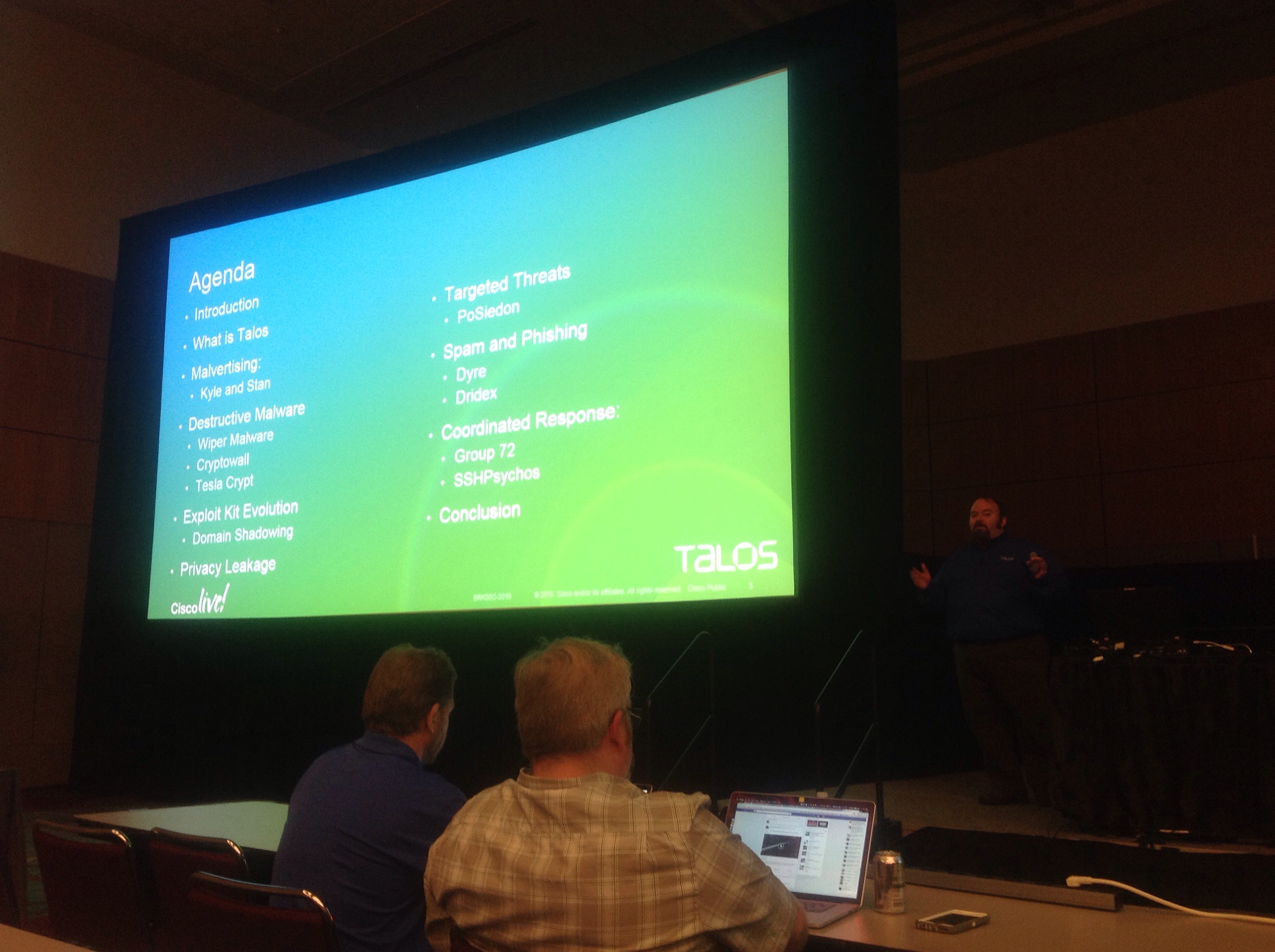
BRKSEC-2010: Emerging Threats -- The State of Cyber Security
Presenter: Craig Williams (@security_craig) - Sr Technical Leader / Security Outreach Manager, Cisco TALOS
"I'm from Talos. We love to stop bad guys."
- 1.1 million incoming malware samples per day
- 1.5 billion Sender Base reputation queries per day
Talos has a serious amount of data. For serious.
Data is key. It allows generation of real threat intel.
"We basically have a bottomless pit of data"
Talos vuln dev team:
- Looking for ways to programmatically find 0-days
- Takes this research and feeds it back into Cisco to a) make Cisco products more secure and b) generate sigs and threat intel to protect customers
With ransomware, you're basically funding the malware underground.
Malvertizing:
- Malicious ads which redirect user to malware and then infects them
- Kyle & Stan campaign dynamically generated a new .exe every time it was downloaded; prevented matching on the file hash; Cisco AMP can stay on the bleeding edge of this
- blogs.cisco.com/security/talos/kyle-and-stan
Destructive/Wiper Malware:
- Targets your data
- Not just file data, but also seen targetting network devices and wiping their configs
- Cryptolocker 2.0: uses TOR for C&C; encrypted binary to avoid hash fingerprinting; anti-VM check
- Cryptolocker 3.0: still encrypted binary; still uses ToR and also I2P; no more anti-VM check
- blogs.cisco.com/security/talos/cryptowall-3-0
- TeslaCrypt: author's error; actually uses 256 bit AES crypto, not RSA asymetric. Same key that encrypts also decrypts. Talos wrote a tool which, if the key is still on the infeced machine, can decrypt the files
- http://blogs.cisco.com/security/talos/teslacrypt
Security products that use only hashes to check for known malware is a FAIL. Modern malware is using techniques to get around those products.
An Internet Explorer 0-day has a six-figure value [in the underground marketplace]
Privacy Leakage:
- Private data can be leveraged in further attacks; make phishing attacks contextually relevant
Point of Sale Malware:
- PoSeidon - the attack started via lateral movement and recon; didn't rely on 0-day to get into the environment at fist, just hard work
Coordinate Response:
- Shutting down Group 72 threat actors - around since 2004 (!!); ZxShell malware
- SSHPsychos - brute force SSH servers using a large list of passwords; goal was to built a large botnet; 1/3 of all ssh traffic on the internet attributed to this botnet
- blogs.cisco.com/security/talos/sshpsychos
For more information: